What determines risk?
The Office of Cybersecurity has worked with many of our campus partners to assess the risk of using new and unknown vendors and their tools. One of the most difficult questions we must answer is “When do I have to do a risk assessment?” Most of the time, our response is “It depends.” Unfortunately, that is not a very helpful or quantitative response.
To try to clarify our process for assessing risk, we asked ourselves, as a team, “What does the risk depend on?” Below you will find a summary of the key components.
What does the risk depend on?
Scope and data classification are the most important pieces of information when deciding on whether or not to assess risk. Data flow will then impact the decision and may move it towards or away from an assessment .
These factors together, and many more, are the basis for determining risk.
Key determining factors
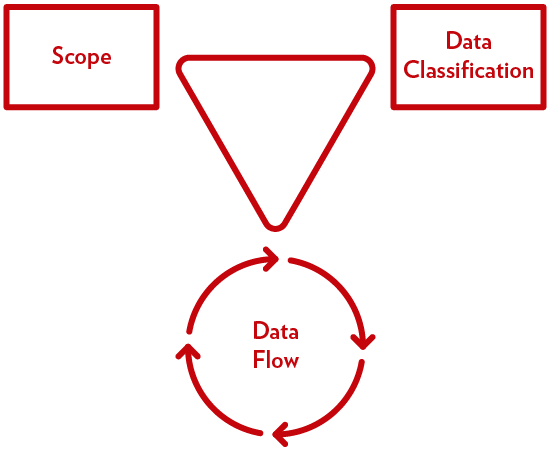
Risk depends on the relationship between scope, data classification, and data flow as it pertains to RMC.